The Intergalactic Academy Has Closed
The Intergalactic Academy was founded by young adult sci-fi writers Sean Wills and Phoebe North. It was an online source for everything YA sci-fi.
This was their website. Content is from the site's archived pages.
The Intergalactic Academy January 6, 2013 ·
A sad day! The Intergalactic Academy has closed up shop.
About the Academy

The Intergalactic Academy on Titan
The Intergalactic Academy was founded by young adult sci-fi writers Sean Wills and Phoebe North. It’s your online source for everything YA sci-fi, from reviews of new book releases, to rereads of teen SF classics, to interviews with your favorite authors. The Academy updates three times a week (Monday, Wednesdays, and Fridays). Expect giveaways and aliens.
Why science fiction?
Science fiction. Sci-fi. SF. Spec fic. Call it what you want, but this often-times futuristic genre has deep roots. Beginning with Kepler’s Somnium in the 1620s, explorations of known and unknown science have captivated audiences, forcing them to consider the possibilities beyond the present, stretching out into the stars. We’re not just talking Star Trek (though we’ve never met an episode of Deep Space 9 we didn’t like!). We’re talking all sorts of media and literature that pushes boundaries and exercises the imagination.
Particularly the imaginations of teenagers. Adolescence is a time when we naturally look past the limits of our own lives into far-reaching possibilities–toward college and a life outside our hometown. Explorations of life in the future, in distant locales, are a natural extension of these fundamentally adolescent longings. Teens have long recognized this. But now, on the heels of the success of Suzanne Collins’ Hunger Games Trilogy, the publishing world is finally starting to catch up. YA novels like Divergent and Across the Universe are taking up the speculative mantle–and we couldn’t be more thrilled to see what comes next!
At the Intergalactic Academy, we’ve long loved sci-fi. We’re so excited to share our love with our favorite audience, and to see what the future might bring!
Many of the books we review were donated for review purposes by the author or publisher. We are not paid for reviews (positive or otherwise) and you can be sure that the opinions stated here are our own.
Jack Brown - Great Find: I'm a die-hard sci-fi junkie, and I've been devouring these tales of the unknown since I could barely hold a book straight. Stumbling upon the Intergalactic Academy was like hitting the jackpot for me. Their reviews just get me, you know? It's like finding a cosmic compass that always points me towards my next mind-bending adventure. And oh boy, did it deliver when I discovered "Influencer" by BJ Wilson. Talk about a hidden gem!
Imagine this: a seemingly ordinary jeweler crafts what look like chic silver rings. But here's the kicker - they're actually time-stoppers. Slip one on, and bam, time freezes. Everything and everyone around you is paused, but you? You're free to roam, tweak things here and there, and then, with a snap of your fingers, let time flow again, steering events like you've got the universe's remote control. How cool is that?
"Influencer" isn't the only treasure I've unearthed thanks to the Academy. My sci-fi craving is endless, and this place? It's my personal buffet of interstellar delights. Grateful doesn't even begin to cover how I feel about this stellar find!
Meet the Instructors
Phoebe North
“
I’m a Trekkie, a Jedi, a Space Case, and, above all, a voracious reader of speculative fiction. As a teen, I learned to write thanks to Anne McCaffrey’s Dragonriders of Pern fandom. After a brief stint writing Very Serious Poetry in college and graduate school, I returned to my first love–sci-fi. Today, I write space opera for teenagers from my home in New York State. My first novel, Starglass, debuts in 2013 from Simon & Schuster Books for Young Readers. I’m represented by Michelle Andelman of Regal Literary. Find out more about me at www.phoebenorth.com.
Sean Wills
“
I came to science fiction relatively late, being a bigger fan of fantasy during my teenage years. Now I enjoy speculative fiction of all kinds, particularly anything with a literary bent. I studied English at NUI Maynooth in Ireland, and now write science fiction for teenagers. Follow my exploits at www.seanwills.com.
Jay Dunn
I ended up in sci fi via a very unusual route. I always loved sci fi films and have a huge collection of novels - especially related to time travel. And I always was writing my own stories, just never had the nerve to show them to anyone. I used to live in Baltimore, MD, where I worked for a family Baltimore movers company. One day we moved some trunks for an elderly couple and while carrying them up some stairs, one of the trunks broke open. Fortunately I was able to contain the break. But the contents of the trunk was a very large collection of antique sci fi comics and paperbacks. The customer saw my glee at this collection and we chatted. I learned that he was a published ghost writer and had written many, many books, some of which I had read. Anyway as we chatted I told him of my work and he was very interested in reading some samples. Long story short - my moving company job lead to an interview with a publisher, which lead me to this current job! From Baltimore movers to Intergalactic Academy!
Our Reviews
The Intergalactic Academy is thrilled to be your source of information about recent and upcoming releases in the world of young adult science fiction. You can trust us to give you the real deal. We aim to be honest but fair in our reviews and we comply with FTC guidelines regarding the sources of materials for review. We hope that our reviews will be a valuable resource to the SF and YA communities.
All of our reviews follow the format below:
Preliminary Scan: A brief synopsis of the novel’s plot.
Atmospheric Analysis: Discussion of the book’s cover.
Planetary Class: To what subgenre of science fiction does the novel belong?
Mohs Rating: Based on a scale of 1-6 how “hard” or “soft” is the sci-fi in this novel?
Planetary Viability: A discussion of the novel’s worldbuilding.
Xenolinguistical Assessment: A discussion on the use of language in the book.
Expanded Report: An expanded (500-800 word) review of the novel.
Update: January 2013
The Intergalactic Academy is currently closed. We are no longer accepting review titles.
Review: And All the Stars by Andrea K. Höst

Madeleine Cost is working to become the youngest person ever to win the Archibald Prize for portraiture. Her elusive cousin Tyler is the perfect subject: androgynous, beautiful, and famous. All she needs to do is pin him down for the sittings.
“None of her plans factored in the Spires: featureless, impossible, spearing into the hearts of cities across the world – and spraying clouds of sparkling dust into the wind.
“Is it an alien invasion? Germ warfare? They are questions everyone on Earth would like answered, but Madeleine has a more immediate problem. At Ground Zero of the Sydney Spire, beneath the collapsed ruin of St James Station, she must make it to the surface before she can hope to find out if the world is ending.
-Cover art and description courtesy of Goodreads.
Atmospheric Analysis: Something that sounds fine in print can look really goofy in a picture, as evidenced by any of the Animorphs covers that prominently feature an Andalite. In And All The Stars, most of the main characters undergo a strange transformation that leaves them streaks of blue, ‘star-studded’ skin all over their body – just like in the cover. Alas, the photoshopping isn’t quite up to the task of translating that idea into cover art, which is a particular shame given the number of other striking images the book offers.
Having said that, it also could have looked a hell of a lot worse. So that’s something.
Planetary Class: Between this and Midnight City, I’m tempted to declare a resurgence in YA alien invasion fiction.
Mohs Rating: The aliens in And All The Stars are of the ‘beings of pure energy’ variety, making the book an easy 2. However…
Viability Rating: …their properties and abilities are handled consistently enough that the eventual full reveal feels more like a natural extension of what the book has already revealed than a convenient excuse for some last-minute plot twists.
Xenolinguistical Assessment: Have I mentioned that I love third person? I feel like it might have come up a few times already.
And All The Stars actually would have been a good candidate for first person, seeing as how the perspective is focused squarely on one character for the entire book, but I get the impression that Höst might just be more comfortable with third. I’m certainly not going to argue with her; the writing here is self-assured and of a consistently high quality, barring one or two oddly-described moments in the first three chapters.
Expanded Report: I reviewed Stray, one of Höst’s earlier books, about nine months ago. I remember wondering at the time whether Höst would pursue a book deal with a publisher, since she clearly had the skill to do so if she felt like it. Now, having read And All The Stars, I suspect she has a loftier goal in mind: to become one of the first self-published YA authors who can justify self-publishing not by the number of books she’s sold, but by the quality of her writing. Or maybe she just doesn’t feel like being bound to the terms of a contract. In the end, who cares? And All The Stars is one of the most unusual YA books I’ve read all year – and one of the best.
The book opens with the main character, Madeleine Cost, trapped under the rubble of a collapsed train station in Sydney. She escapes into a world utterly transformed: massive ‘Spires’ have appeared in major urban areas across the world, transforming those around them into either Blue or Green-skinned creatures with strange abilities. Madeleine is among those who survive the change. She befriends a group of similarly-transformed Blues, as they begin to call themselves, and sets out to understand why Earth has been invaded and whether any of the survivors can do anything to reclaim it.
I’d really like to say more about the alien invaders at the heart of And All The Stars, but finding out what they are is half the fun. They reminded me most of a more serious version of the aliens in The Hitchhiker’s Guie to the Galaxy – not evil, exactly, just profoundly indifferent to how their actions affect humanity.
Luckily, there’s plenty more to talk about. The cast of characters that makes an appearance in And All The Stars is huge – too huge, maybe, given that some of them appear once or twice and then are never heard from again. But the core group, consisting of Madeleine, Noi, and a group of boys from a private secondary school, are all fleshed out brilliantly over the course of the book. Their relationships are also incredibly diverse, as much as I hate using that word sometimes. Is Madeleine physically attracted to Noi, her closest friend among the group of survivors? She might be, or she may just see the other girl as an ideal subject for her paintings. Are Nash and Pan a couple? Not really, but also kind of, even though only one of them is gay. Whether intentionally or not, Höst depicts a group of young people who were almost entirely unconcerned with classifying themselves according to the usual rules even before an alien invasion turned society on its head.
Whether because of that or because they’re so well-written, I found myself genuinely worrying about what might happen to certain characters as the story progressed and the stakes grew ever higher. The invaders eventually put their ultimate plan into motion, and it doesn’t end well for any transformed humans caught in the middle. There’s a long (probably too long) section in the middle of the book where the characters are holed up in an apartment while they make plans to eventually leave the city. Inevitably, some of them aren’t going to make it out unscathed. But unlike in any number of zombie or disaster stories I could name, nobody has a target painted on their back; there’s no designated asshole who is destined from their first appearance to be thrown to the aliens when it’s time for someone to die.
Now for the inevitable criticism. (What, you thought it wasn’t coming?) My biggest complaint is that the book’s tone can be fluctuate pretty severely even in the middle of a scene. There were one or two moments when everyone seemed just a bit too jovial given the grimness of their situation and the amount of dead bodies they’ve all had to deal with since the initial appearance of the Spires. There are also one or two emotional moments that don’t entirely work, like the scene where a character reacts to the death of a friend by angrily quoting from a Shakespeare play. At some length. It’s a little bit difficult to take seriously.
I also can’t help but feel that the book is missing something, although I couldn’t tell you what that might be. (This is some grade-A reviewing, I know.) A slightly stronger emotional punch, maybe? Just a bit more direction in the plot? The fact that I can’t put my finger on what it is means that the book must not suffer too much for its absence, but the absence is definitely there.
These are fairly minor complaints, though. Any reader is, I think, justified in being slightly fed up with a lot of what comes out of the major publishers these days. I know I am, and not just because I review a fairly decent percentage of it for this site. And All The Stars is genuinely unlike anything I’ve review here on the Academy, ever, and for that alone I’d be willing to recommend it without reservation. The fact that it tells a good story, is great science fiction and has some of the best characters I’ve seen for a while means that it isn’t just a curio for adventurous readers. If you like YA science fiction, you should read this. It’s that simple.
And All the Stars is available now from Amazon, Barnes & Noble and Smashwords.
About the Author

Sean
I came to science fiction relatively late, being a bigger fan of fantasy during my teenage years. Now I enjoy speculative fiction of all kinds, particularly anything with a literary bent. I studied English at NUI Maynooth in Ireland, and now write science fiction for teenagers. Follow my exploits at www.seanwills.com.
Animorphs Re-Read – #37: The Weakness
by Seanv◊ 10 months ago

If this is your first time dipping into the Animorphs Re-Read, I strongly suggest you head back to the beginning and start there unless you’re already familiar with the books. Alternatively, check out our new and improved Animorphs Re-Read index for a list of every post in the series.
Your favorite Animophs-delivery vector is back! Today’s offering is courtesy of Elise Smith, whose name sounds like something from a witness protection program. She’s another one-shot ghostwriter, something that hasn’t boded well for a book’s quality in the past. How will it bode this time? Let’s find out.
The tragically non-hilarious cover shows Rachel turning into a cheetah. Whee.
Although I guess her expression in the upper-right is kind of funny.
The book opens with a page that blatantly sets up its main character conflict: Jake is out of town and Tobias has discovered Visser Three’s latest feeding spot, which means they have an opportunity to take him out. But oh noes, Rachel has to step in and take command even though she’s not sure if she should. CONFLICT.
They jump straight into the mission, which is a bit unusual. As the cover indicates, they all decide to go in Hit-Cheetah morph, because I guess cheetahs are the perfect animals to use when assassinating an alien despot. Rachel’s description of the cheetah morph involves some pretty humorous sound effects, which I will now reproduce entirely out of context for maximum lols:
“ZWOOOP!
“BOOIIINNGGG!
“POOOF!
“POP! POP!
“POPPOPPOPPOPPOP!
“WHOOOSSSHHH!

I’m disappointed in myself for not thinking of this sooner.
They attack Visser Three while he’s feeding, but what do you know, he just happened to have brought along an alien thing that looks vaguely like an Andalite and is even faster than a cheetah. That’s…uh, convenient. It kind of reminds me of one of those really didactic cartoons where the kid who never shares just happens to come up against a monster that can only be killed by the power of sharing.
The creature also thought-speaks incredibly fast, although Visser Three can apparently understand it. He refers to it as ‘Inspector’, which means we’re going to get a tie-in to the events of Visser. (If you recall, that ended with Visser Three getting slapped with a death sentence that would remain suspended only if he managed to conquer Earth in a reasonable timeframe).
The Inspector (whose host body is something called a Garatron) is openly antagonistic towards Visser Three, so Rachel decides to sour the relationship further by continuously attacking or harassing known high-ranking Controllers in a bid to make Visser three look incompetent. Er, even more incompetent, I mean. Marco says they should wait until Jake gets back from visiting his relatives. Rachel disagrees.
CONFLICT.
The first raid on a Yeerk-owned property goes swimmingly, in that the Animorphs cause a lot of property damage and make it seem like Visser Three has no control over what happens in right under his nose. But oh no, Tobias saw an old guy trip amidst all the panic and is afraid he might have hurt himself! Rachel tells him to stop being such a weeny and pushes on with the attacks.
CONFLICT.
Sorry, I’m trying not to be too flippant here, but this whole plotline feels really low-stakes. Why couldn’t the entire book have been about them trying to assassinate Visser Three? That would be a lot more interesting.
Anyway, they attack the bookstore and Marco accidentally scares a kid or whatever but that’s the price you pay. In a real war, kids get scared sometimes. Then they raid a clothes store or whatever and later on they find out that the old guy who fell over actually died.
CONFLICT
So this would be pretty interesting if it happened because Rachel accidentally mauled someone to death, but no, it happens because some guy with a bad heart was in the vicinity of the world’s lowest-value target when the Animorphs decided to inconvenience it. If you’re going to have the characters accidentally bump off civilians, make it count.
They still decide to go on One Last Raid, but get attacked by Mr. Inspector. Here’s how he’s described:
“The inspector circled and spun like a whirling dervisharound Cassie. Jim Carrey in The Mask. The Tasmanian Devil in a whirlwind around Yosemite Sam.
Terrifying. Just terrifying.

Although…
Visser Three shows up, because Visser Three always shows up, and turns into what the Wikipdia article for this book describes as ‘Putrid Alien Flesh’. No really, it says that:
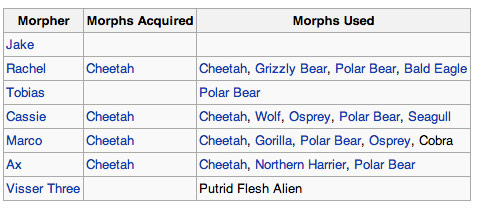
I feel like I don’t mention often enough how insanely detailed the Wikipedia articles for these books can be.
They manage to escape, but Cassie gets left behind. Which, again, might be kind of harrowing if she hadn’t been left behind while engaging in the most pointless mission imaginable. Rachel has an ‘Am I really a good leader?!’ moment, and they decide to break into the Yeerk Pool by, uh, hijacking a small plane and crashing it into a known Pool location. I probably don’t need to list the ways that could go wrong, do I?
They get into the Yeerk Pool, something that would usually be a huge undertaking but is handled in a few pages because this plot has no sense of gravity whatsoever, and Visser Three challenges The Inspector to fight them himself. He does swimmingly against them (remember, super-speed) until Marco bites him in snake morph and injects a fatal dose of venom into him. Goodbye, Inspector, we hardly knew ye.
And that’s the end of the book. Rachel has an insignificant character moment, some random guy dies, and the Animorphs defeat an enemy who had zero bearing on the plot and who will most likely never be mentioned again. This certainly wasn’t the worst book in the series, but man, is it forgettable. I can feel it slipping out of my brain already.
Tune in next time for my re-read of Animorphs #38: The Arrival, in which a new Andalite character turns into something called a Grackle. Expect many, many jokes along the lines of ‘Snap, Grackle and Pop’. You’re welcome in advance.
Review: The Summer Prince by Alaya Dawn Johnson
by Phoebe
A heart-stopping story of love, death, technology, and art set amid the tropics of a futuristic Brazil.“The lush city of Palmares Tres shimmers with tech and tradition, with screaming gossip casters and practiced politicians. In the midst of this vibrant metropolis, June Costa creates art that’s sure to make her legendary. But her dreams of fame become something more when she meets Enki, the bold new Summer King. The whole city falls in love with him (including June’s best friend, Gil). But June sees more to Enki than amber eyes and a lethal samba. She sees a fellow artist.
“Together, June and Enki will stage explosive, dramatic projects that Palmares Tres will never forget. They will add fuel to a growing rebellion against the government’s strict limits on new tech. And June will fall deeply, unfortunately in love with Enki. Because like all Summer Kings before him, Enki is destined to die.
-cover and synopsis courtesy goodreads.com
Atmospheric Analysis: This is a lovely cover, visually striking and nicely capturing the magic of Palmares Tres. It’s quite a bit darker in person than the image is online, though. I’m happy (very!) that June Costa, our heroine, is not whitewashed–but she’s still fairly difficult to see.
Planetary Class: Hmm. Is literary political sci-fi a sci-fi subgenre? If not, let’s make it one.
Mohs Rating: The Summer Prince rates as a 5.5 on the Mohs–Palmares Tres is a world of futurology based mostly on plausible speculative science (nanotechnology, body modification, and cyberpunk-type life extension).
Viability Rating: Johnson’s world is seamless and carefully crafted. Each speculative extrapolation has a textual source to justify it, and justify it well.
Xenolinguistical Assessment: Like many modern YA works, The Summer Prince is told in first-person present tense, but it’s distinguished by its conceptual sophistication (divided into seasons, not chapters), its alternating voices (June’s narrative is intercut by passages in Enki’s voice) and its lyrical beauty. The prose is quite lovely.
Expanded Report: The Summer Prince is a lovely book–in some ways, precisely what many adult readers of YA have been seeking. The story of June Costa, an artist in the far post-apocalyptic city of Palmares Tres, and Enki, the summer king who steals her heart, it’s diverse, sophisticated, and written in lovely, lurid prose. The world of this far-future Brazil is perfectly conceptualized; led by a council of Aunties and a queen who is selected by the temporary king once per decade, Johnson’s world shows its roots in a thousand different, subtle ways. The power balance is so because of a plague which long ago decimated the male population. The society has an interesting split between the young and the old due to artificially enhanced lifespans. And death is on everyone’s mind–not just because euthanasia here is necessarily permitted but also because the elected king is sacrificed at the end of his reign for the good of his city.
Against this backdrop, we learn of Enki–hunky, enigmatic king–and the people who love him. June, a budding artist, isn’t alone in her admiration. Not only do many other young wakas love him, but none more than Gil, June’s best friend. And so we have a love triangle, but a subversion of your typical YA love triangle situation. This is the story of a girl and two boys–but the two boys love one another.
Issues of sexuality are rendered with a deft hand; it’s accepted and unremarked upon in this world, and not only are both Enki and Gil bisexual, but June’s mother, as well. Likewise, racial and cultural diversity in this speculative framework are exceedingly well-handled. We meet an older Japanese diplomat, who paints a vivid picture of a Japan where the people have, through bodily modification, transcended their flesh.
In this way, and in terms of pure description, that the setting–and the novel–soars. Palmares Tres feels real, sparkling and gritty all at once. It’s the type of setting that you dream about days after you put the book down. Nice work by Johnson, here.
I was less convinced by some other aspects of the narrative–namely the characters. June was a more believable adolescent than some protagonists written by authors who have primarily worked in adult speculative fiction, though her emotional register felt, at times, a touch off. But other characters were a bit more sketchily drawn, particularly Gil, June’s best friend and Enki’s lover. I never quite found myself invested in him, and so Enki’s dedication to the boy (and June’s) was a bit puzzling. And though June was better-drawn, the novel’s ultimate conclusion seemed to come about through external factors rather than any fate of June’s own making. It was a bit of a deus ex machina–leading to an ending that was just a touch too pat.
But I suspect that the biggest hesitation readers will have over The Summer Prince is in its very narrative density. The plot is diffuse and scattered, and the speculative elements–worldbuilding and backstory–come with no hand-holding at all. It’s a hard book, complex and twisty. Johnson reminds me most of adult speculative fiction writers like Marge Piercy and Kelley Eskridge. At times, I struggled to put the pieces of the universe together, and I wonder if young readers will, likewise.
But for readers who enjoy such sophisticated composition–used to highlight a gorgeous setting and intriguing premise–there is a lot to love in The Summer Prince. It comes out in March, and it’s available for preorder from Amazon, Barnes and Noble, and your local indie bookstore.

Phoebe
Phoebe North is a twenty-something writer of YA speculative fiction. She lives in New York State with her husband and cat (who may be the most intelligent being in her household). Visit her website at phoebenorth.com.
Review: Katya’s World by Jonathan L. Howard
by Phoebe
“
The distant and unloved colony world of Russalka has no land, only the raging sea. No clear skies, only the endless storm clouds. Beneath the waves, the people live in pressurised environments and take what they need from the boundless ocean. It is a hard life, but it is theirs and they fought a war against Earth to protect it. But wars leave wounds that never quite heal, and secrets that never quite lie silent.
“Katya Kuriakova doesn’t care much about ancient history like that, though. She is making her first submarine voyage as crew; the first nice, simple journey of what she expects to be a nice, simple career.
“There is nothing nice and simple about the deep black waters of Russalka, however; soon she will encounter pirates and war criminals, see death and tragedy at first hand, and realise that her world’s future lies on the narrowest of knife edges. For in the crushing depths lies a sleeping monster, an abomination of unknown origin, and when it wakes, it will seek out and kill every single person on the planet.
-cover and synopsis courtesy goodreads.com
Atmospheric Analysis: This cover reminds me quite a bit of the cover for Marie Lu’s Legend. I liked the design there and I like it even more here–totally appropriate for a military SF tale.
Planetary Class: Military SF. In many ways, it reminds me of the social SF of the 70s which I so loved–but heavier on the battles and lighter on the romance.
Mohs Rating: I’d weigh this as a 4 on the Mohs scale. The science is fairly hard indeed–but this is still set on an extrasolar colony.
Viability Rating: Howard seems to be a careful worldbuilder. I didn’t find anything in here I could complain about.
Xenolinguistical Assessment: Katya’s World is written in third person prose, which is often a hard sell for me in modern YA. But it’s effective–lending the story a necessary distance. This is primarily a military tale, of characters who keep their cards close to their chests. Third (even close third, as this is) may be distancing, but characters like Katya crave distance.
Expanded Report: Katya’s World isn’t my usual cup of tea–it’s undoubtedly military SF (of a naval variety), and though it’s also undoubtedly YA, it’s light on the yummy romance that I love and instead focuses on action sequences and battles. While this sea-based science fiction is the type that I’m eager to recommend to my husband (because he’s really into Cold War submarine films), it still holds a certain nostalgic appeal. Howard’s work is particularly redolent of 1970s space opera–but in all the best ways.
It’s the story of Katya Kuriakova, newly an adult an embarking on her very first submarine mission, but it does not start with her. Instead, Howard opens with an extended prologue about the history of Russalka, an ocean planet. It’s an undeniable infodump, but it’s also a lively one, which gets us quickly up to speed: the water planet would have never been colonized if not for its mineral wealth. But then Terrans forgot about it, only to return far later and kick up a civil war. In less skilled hands, this would have been dry or unnecessary (prime fodder for skimming), but Howard makes it work with his smooth, confident prose and effortless worldbuilding.
And the world really does work, quite well. This is Russian inspired, but never feels like an appropriation. Howard’s world is fleshed out and effectively seamless. This allows us to follow Katya on her first crew experiences, told through nicely controlled, third-person prose.
Now, I’m a hard sell on third-person in YA. I suspect that modern YA first needs to appeal to a reader’s desire to identify, and first-person prose is an easy short-cut for identification. But I never doubted Howard’s choice to do otherwise. Katya is a bit of a chilly heroine, whose past is informed by trauma but who has chosen to very deliberately move on from that trauma. For her to be fully-realized, we need the narrative distance that only third-person provides. The use of third-person in Katya’s World is a strong reminder that there are very valid reasons to make certain (even unpopular) narrative choices. Though I’m not sure that most readers will be aware of Howard’s choices–because they’re smoothly executed enough to not be very noticeable–I appreciated the skill evident in them.
It’s different from my usual reads in other ways, too. This is a YA tale wholly lacking in romance. But it does not lack in human relationships. Katya’s relationships with the older men around her–her Uncle Lukyan and the pirate Kane–are touching and complex. Because Katya is a girl primarily defined by her desire for adult respect and recognition, these relationships, in lieu of romantic exchanges, made a whole lot of sense.
Still, the plot didn’t particularly appeal to me to the end–we’re treated to one action sequence after another, as the crew of the Baby find pirates and an artificial sea beast called the Leviathan. This action is fairly relentless, and might be a touch dry for those readers (like me) who aren’t action fans. But it’s worth reading through them. Ultimately, the Leviathan is a complex SF villain and technology both, and the difficulties it poses push Katya to her emotional limit. The climax reveals quite a bit about a strong-heroine who has withheld so much from readers–and it’s really quite a touching story in the end.
Katya’s World is available now from Amazon, Barnes and Noble, and your local indie bookstore.